Fortifying APIs: Implementing Robust Query Parameter Validation
Building reliable and secure APIs starts with trust, and in the world of distributed systems, trust is built on rigorous validation. For the name-profiler-api service, ensuring that incoming requests are well-formed and adhere to expected parameters is paramount to maintaining stability and providing clear feedback to clients.
The Challenge of Untrusted Inputs
Every external input to an API is a potential point of failure or vulnerability. Without proper validation, an API might encounter:
- Type Errors: Receiving a string when an integer is expected can lead to server-side exceptions.
- Out-of-Range Values: A
limitparameter exceeding acceptable bounds could trigger resource exhaustion. - Logical Inconsistencies: A
max_agevalue less thanmin_agecreates an impossible query. - Unrecognized Parameters: Unexpected parameters can indicate misconfigured clients or attempts at injection, leading to unpredictable behavior.
Such issues degrade API reliability, complicate debugging for client developers, and can even expose the system to security risks.
A Comprehensive Validation Strategy
To address these challenges for the GET /api/profiles endpoint, a comprehensive query parameter validation layer was introduced. This layer meticulously checks each incoming parameter against a predefined set of rules, ensuring data integrity and predictable behavior.
The validation covers several key areas:
- Parameter Whitelisting: Only explicitly allowed parameters (e.g.,
gender,age_group,country_id,page,limit,sort_by,order) are accepted. Any unrecognized parameters result in a400 Bad Request. - Type and Value Constraints:
page: Must be a positive integer.limit: Must be an integer within a specific range (e.g., 1-50).min_age,max_age: Must be non-negative integers, with an additional logical check thatmax_ageis not less thanmin_age.
- Enum Checks: Parameters like
sort_byandorderare restricted to a predefined set of values (e.g.,age,created_at,gender_probabilityforsort_by;asc,descfororder). These checks are also case-insensitive for user convenience. - Probability Range:
min_gender_probabilityandmin_country_probabilitymust be floating-point numbers between 0.0 and 1.0, inclusive. - Database Existence:
country_idis validated against existing records in the database to ensure only valid country identifiers are used.
Clear Error Feedback
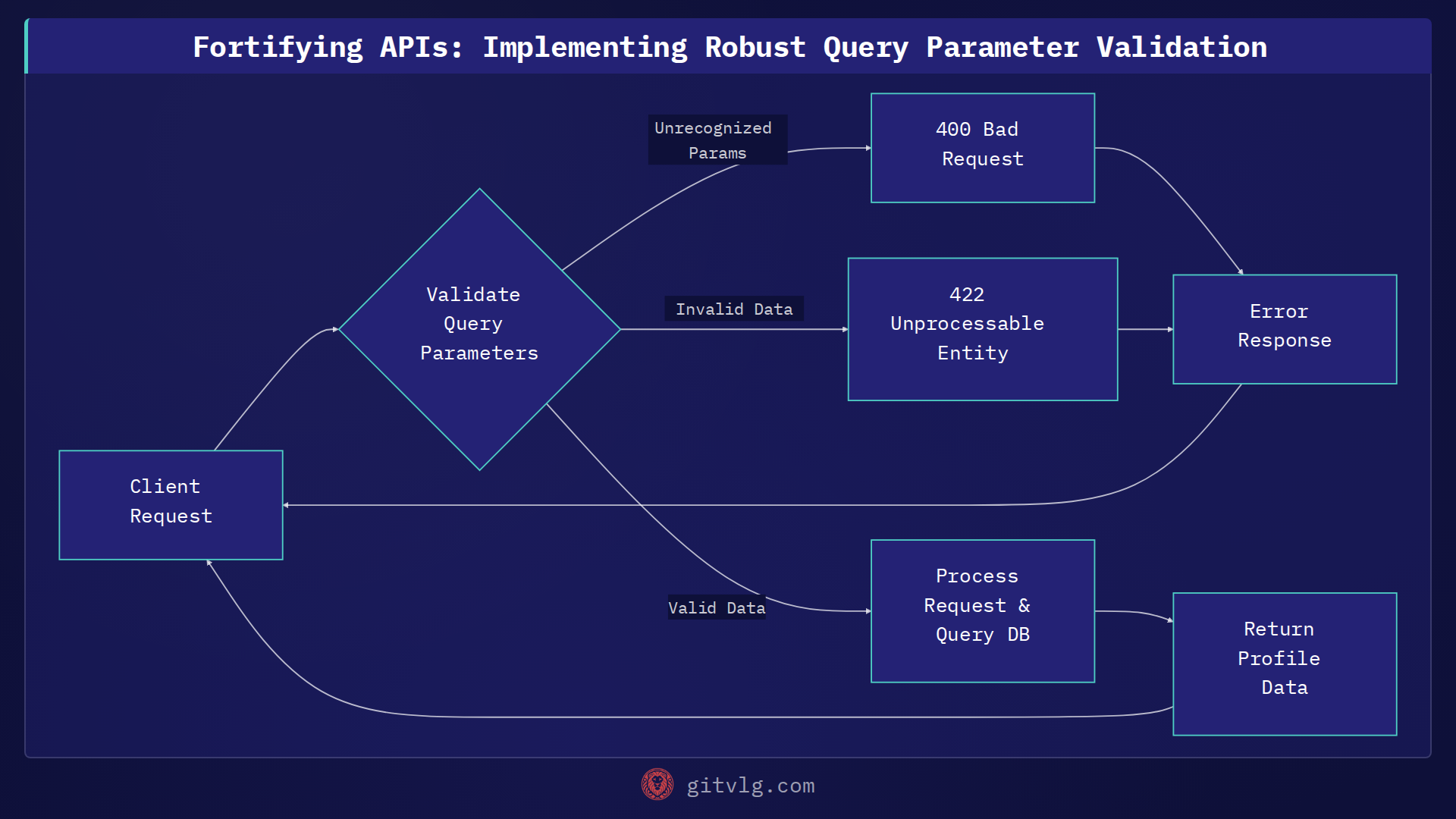
When validation fails, the API responds with specific HTTP status codes and a consistent error format, enabling clients to quickly diagnose and correct issues:
400 Bad Request: Used when unrecognized query parameters are supplied.422 Unprocessable Entity: Issued for invalid parameter types, values out of range, logical inconsistencies (e.g.,max_age < min_age), or when acountry_iddoes not exist in the database.
All error responses follow a standardized JSON structure:
{
"status": "error",
"message": "Invalid query parameters"
}
This predictable error format simplifies error handling on the client side.
Illustrative Code Example
In a Python API, such validation might be implemented using a framework's built-in features or a dedicated validation library. Here's a conceptual example using a Pydantic-like approach:
from pydantic import BaseModel, Field, validator
from typing import Optional
class ProfileQuery(BaseModel):
gender: Optional[str] = Field(None)
age_group: Optional[str] = Field(None)
country_id: Optional[str] = Field(None)
min_age: Optional[int] = Field(None, ge=0)
max_age: Optional[int] = Field(None, ge=0)
min_gender_probability: Optional[float] = Field(None, ge=0.0, le=1.0)
min_country_probability: Optional[float] = Field(None, ge=0.0, le=1.0)
sort_by: Optional[str] = Field(None, pattern=r'^(age|created_at|gender_probability)$', case_sensitive=False)
order: Optional[str] = Field(None, pattern=r'^(asc|desc)$', case_sensitive=False)
page: int = Field(1, gt=0)
limit: int = Field(10, ge=1, le=50)
@validator('max_age')
def validate_max_age(cls, v, values):
if 'min_age' in values and v is not None and values['min_age'] is not None and v < values['min_age']:
raise ValueError('max_age cannot be less than min_age')
return v
# In a real app, country_id validation would involve a database lookup
@validator('country_id')
def validate_country_id_exists(cls, v):
if v and not is_country_id_valid_in_db(v): # Placeholder for DB check
raise ValueError(f'Country ID "{v}" does not exist')
return v
def is_country_id_valid_in_db(country_id: str) -> bool:
# Simulate a database check
valid_ids = {"US", "CA", "GB"}
return country_id in valid_ids
# Example usage in an API endpoint handler:
def get_profiles_endpoint(query_params: dict):
try:
validated_query = ProfileQuery(**query_params)
print(f"Valid query: {validated_query.dict()}")
# Proceed with database query
return {"status": "success", "data": []}
except Exception as e:
return {"status": "error", "message": str(e)}
# Test cases (illustrative)
# print(get_profiles_endpoint({"page": 0})) # Invalid page
# print(get_profiles_endpoint({"sort_by": "invalid"})) # Invalid sort_by
# print(get_profiles_endpoint({"max_age": 10, "min_age": 20})) # max_age < min_age
The Outcome: A More Reliable API
By implementing thorough query parameter validation, the name-profiler-api significantly improves its robustness and user experience. It proactively prevents invalid requests from reaching core business logic, reducing the risk of server errors and unexpected behavior. This not only makes the API more reliable but also provides clearer, more immediate feedback to client developers, streamlining their integration process.
Actionable Takeaway: Always prioritize API input validation as a foundational element of your API design. Comprehensive validation, including whitelisting, type/range checks, and logical constraints, coupled with explicit error messages, is key to building dependable and user-friendly services.
Generated with Gitvlg.com